Dears,
Does any of you managed to encrypt the password used in a batch file when creating a tenant backup ?
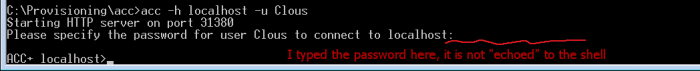
The command line is this one:
E:\SoftwareAG\ARIS9.7\server\acc\acc.bat -c "E:\SoftwareAG\ARIS9.7\server\generated.apptypes.cfg" -h localhost -p 9001 -u Clous -pwd g3h31m -f "E:\SoftwareAG\ARIS9.7\accBackupCmd.txt"
But the g3h31m password is in clear text !
When calling the arisadmintool however we can specify the encrypted password:
E:\SoftwareAG\ARIS9.7\tools\ArisAdm\arisadm90.exe -l $current_dir\dbbackup.log -s localhost:80 -t default -u system "{crypted}072744af76f96c90c302b0a24f8976fe" backup all "$current_dir\"
Any ideas ? ...
Thanks